Xalteox: Sorta.
The ISP is your mailman. They need to get packages to where they need to go, Reddit for example is sending you a package containing this reply. You pay the mailman monthly for a rate at which they send packages from you and to you.
HTTPS encrypts the package’s contents, however the ISP’s responsibility is still to move the package from A to B, and therefore needs to know what these A and B are. Therefore the postage address cannot be encrypted, and your ISP can track who you are exchanging packages with, be it Reddit or YouTube or Netflix.
So your ISP can’t actually see what you are viewing on Reddit, YouTube, or Netflix, but they can see which sites you are accessing.
Loki-L: HTTPS is not a perfect solution. It prevents them from seeing what messages are exchanged but not from seeing who exchanges those messages.
They can see that you are on reddit but not which subedits you are viewing for example.
There are additional things they can see. For example some researches a while back for example showed that you could still recognize which movies a person was watching despite them being transmitted via https. The transmission itself was encrypted, but observers could still see the size of the packets transmitted and match those with what they new about the movies in netflix’s library.
So https is good for not having the entire world see your password when you transmit it, but if you don’t want your ISP to know that you are visiting wws.comcast-sucks.com they won’t help you at all and in some special cases they might in theory learn much more about your browsing habits than you would want them to.
no_real_username: It sort of does. Your ISP cannot read HTTPS data you send or receive (for the most part)
But when you send data, they can see where it’s destined for. When you receive data, they can see where it came from. So they can generally tell which websites you visited. But they can’t tell what you *did* on those sites.
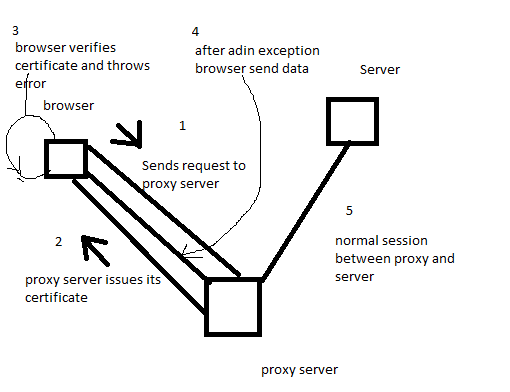
There are a couple of ways they can *sometimes* snoop on your HTTPS traffic however.
If you install one of their certificates, they can potentially act as a man in the middle, reading everything you send and receive. But that requires you to manually install this certificate. It can’t be done silently just by visiting a website. Alternatively, if the website has a non-HTTPS landing page, they can potentially manipulate that so that you are never forwarded to the HTTPS version.
But yeah, assuming your PC isn’t compromised, and the *entire* site runs HTTPS, then the ISP can only tell where data packets are going and coming from, not what’s in them.
Halvus_I: I want to point out that my isp actually will perform man in the middle attacks to send copyright notices. I was torrenting one night and my browser wouldnt connect to https reddit. After a few seconds i got redirected to a ‘copyright violations are bad, click here to restore your internet’ page. Realistically, i should be able to charge them under the CFAA for that. I couldnt believe they would stoop to MITM for copyright…..
TigTanq: They know the IP address you’re sending/receiving information from, not the content. Quite literally just like properly addressed mail through the post office.
Supersnoop25: How does this change on a vpn?
[deleted]: [removed]
Redrundas: I was actually looking into this the other day after my internet was slowed the day after I made a huge download. Turns out it was unrelated. However I found some interesting info about how service providers can determine your online activities without actually seeing the queries of your URLs.
For example, when you’re streaming a video, there is a specific bandwidth usage pattern that is easily distinguishable from downloads and stuff.
[Here](https://imgur.com/gallery/UMcZf) is a diagram representing streaming network traffic pattern.

When a video is buffering, it’s pre-loading part of the video so that it can be viewed without any hiccups. Normally videos will give around 15 seconds of buffer time. When the video comes too close to the non-buffered part of the video (the rest of the video) the bandwidth will be used once again to buffer the next 15 or so seconds of the video. This results in a choppy, zipper-like bandwidth usage pattern. (See the hyperlinked article for a diagram).
While service providers might not necessarily be able to see what you are viewing exactly, by combination of the general address of the website, and the bandwidth pattern. They can usually make a pretty good guess as to what you’re up to. And with all the data they are collecting at the same time, it’s only becoming easier.
Edit: replaced link to article to simply just a link to the diagram
white_hat78: This is the best link I have ever seen.
https://www.eff.org/pages/tor-and-https
Basically, when you send information, like others have said, it gets put into a package, like a box. As the box goes from device to device, each device can add a box and put a sticker label on it. Some devices open the outer box package to read the label on inner boxes. Kinda like how you can recognize a home depot box, these labels and boxes are recognizable. And because it’s all electronic, it’s easy to build a software that can open and read those quickly and do all sorts of analytics. The very inside package might not get opened, but there’s a lot of info you can gather to make very educated and statistically proven guesses in the worst case scenario, and when you compare it directly to other known packages from non encrypted sessions, it becomes a matching game.
idgarad: They can see the volume. If you go to Pornhub for example and watch a video, you are going to pull down data from the video yeah it is encrypted, yeah it is streaming. If the video is exactly 14,586,304 bytes how many possible videos on the site are exactly 14,586,304 bytes? Even streaming wise with enough sample data you can peg what they are streaming. Go to a download site, same thing. I can’t tell what you downloaded but I can see how much you downloaded. How many possible files on the site match the size? The ads are a different connection and unless a website has a substantial random amount of data on each page, it’s easy to gauge what you are looking at. You can never get 100% but you can say “Out of 6 million videos there is a 98% chance he watch video A, 87% chance it was Video B, and 76% chance it was video C.
ReshKayden: The content of your transmission is encrypted, but the address you are sending that information to/from cannot be, because your ISP still needs to know where to send the data.
The problem is that many sites include a lot of information about what you’re doing in the address. For example, this topic on Reddit is at “https://www.reddit.com/r/explainlikeimfive/comments/7eq094/eli5_how_is_it_possible_that_isps_can_see_what/” and none of that is encrypted. Meaning the ISP knows exactly what you’re reading.
If you go to reply to a particular comment, that information is also in the address. So they can also tell that you’re replying, if not precisely what the content of your message was.
Thing is, once you know all this over time, and can track exactly what sites someone is reading/writing to, you don’t even really NEED to know exactly what they wrote. You can guess it with 90% accuracy, which is good enough to then sell to advertisers and third parties.
Delta_Zulu: I’ve always thought of the post card anology. In http You exchange information with a web site in post cards. Everyone who handles your post card can read it.
With https it’s like using an envelope. They still know the address but not the content.
The main thing to remember is that the website address is still visible. So even if your communication is encrypted going to https:reddit.com/r/Am_I_Pregnant tell the ISP a lot
skilliard7: The data is encrypted, but they still have the information in the TCP/IP header to know where you’re connecting to and where you’re connecting from. Without it they wouldn’t be able to route your packets from your computer to the destination and vice versa.
Technique with speed
Source
CurlsontopofCurls: He could have been on Minute to Win It!
BLYNDLUCK: This kid just achieved more then I will in my whole life.